Performance
RAM Memory Usage
| Program | Memory |
|---|---|
| Hash Manager 1.2.3 | 25MB cracking 1 million NTLM |
| John-1.8.0.2-bj* | 98MB cracking 1 million NTLM |
| John-1.8.0.2-bj | 113MB cracking 1 million NTLM |
| Hash Suite 3.5 | 115MB cracking 1 million NTLM |
| EGB 3.2 | 171MB cracking 1 million NTLM |
| Hashcat 4.1 | 979MB cracking 1 million NTLM |
| Cain 4.9.52 | 1073MB cracking 1 million NTLM |
Disk Usage
Hash Suite 3.5 database file with 1 million NTLM hashes and 1 million LM hashes: 80MB
CPU/GPU Usage
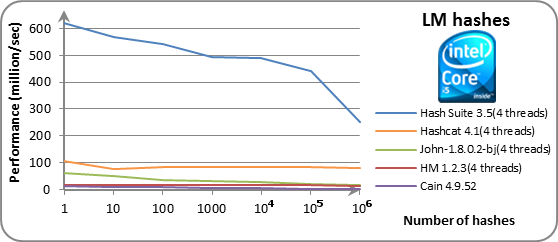
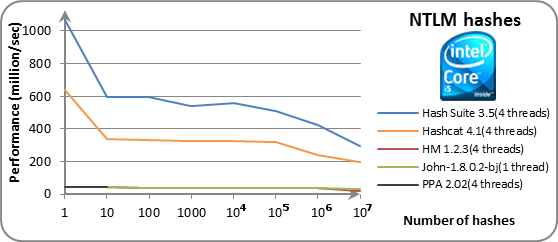
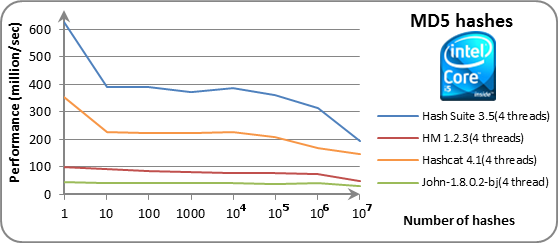
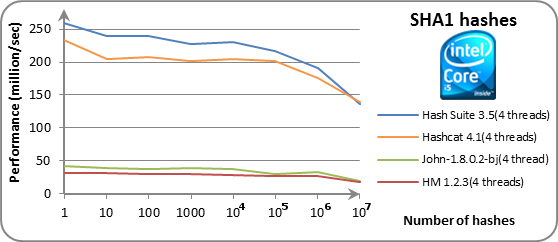
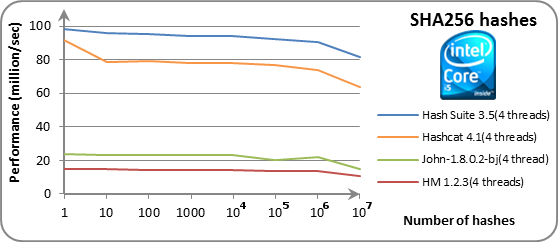
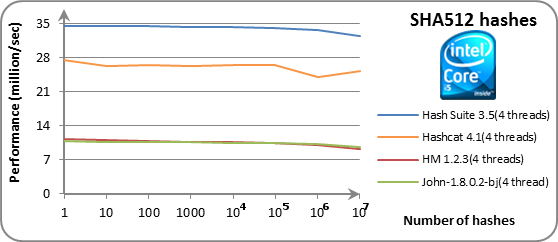
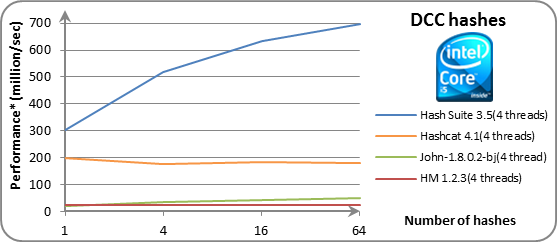
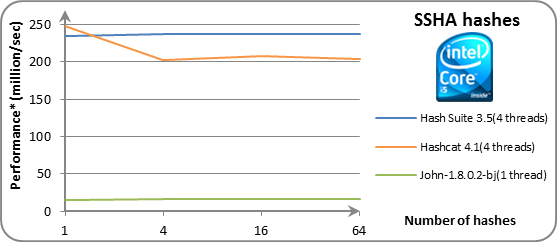
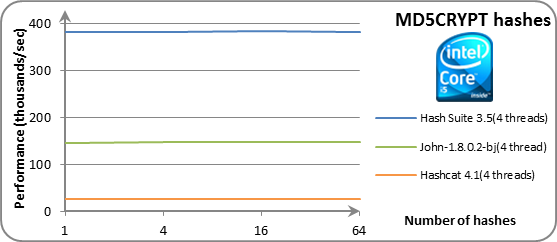
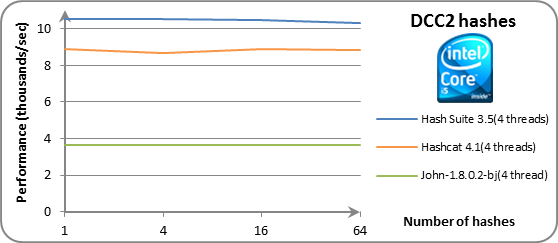
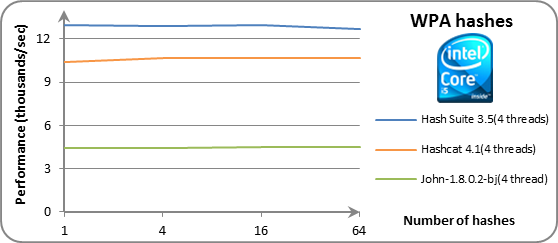
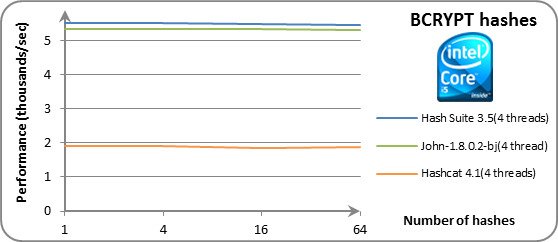
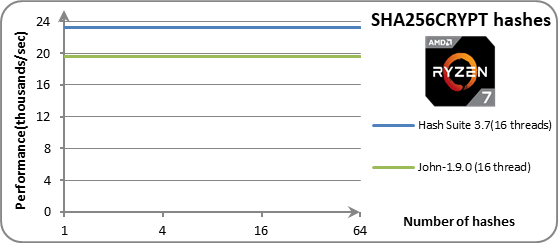
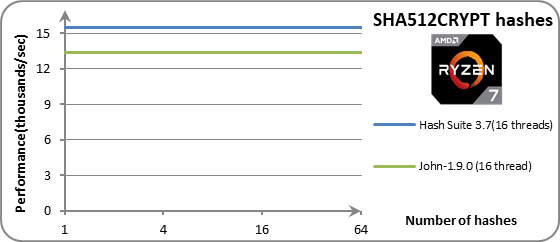
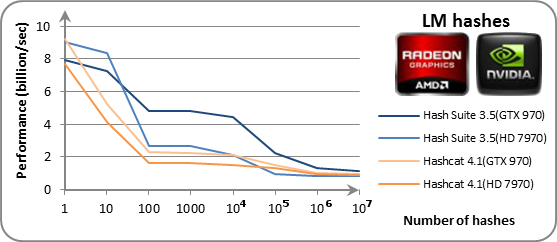
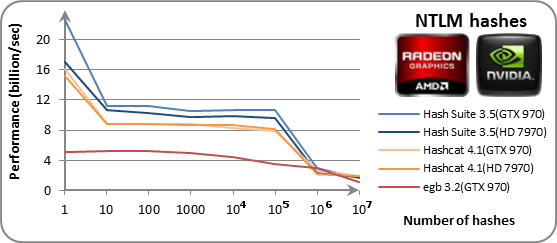
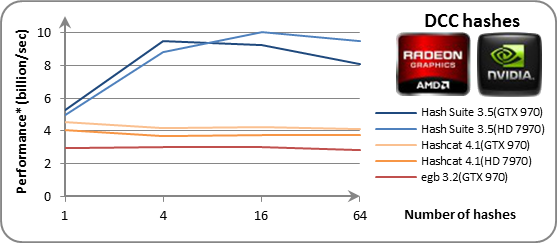
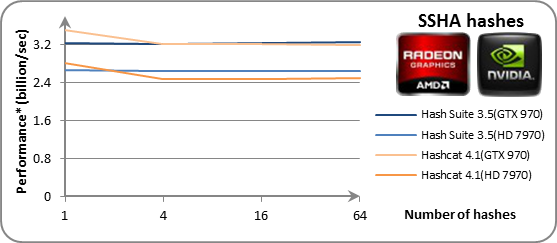
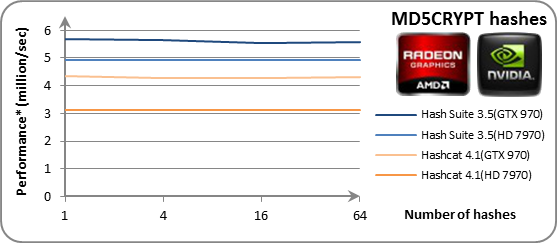
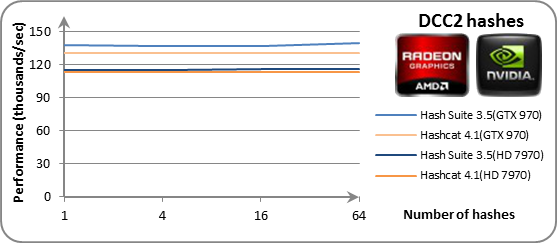
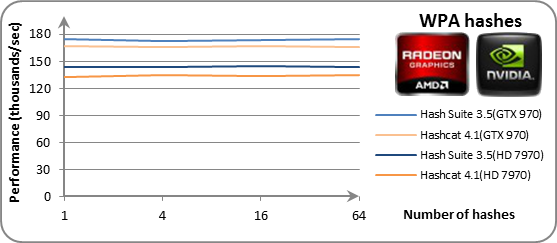
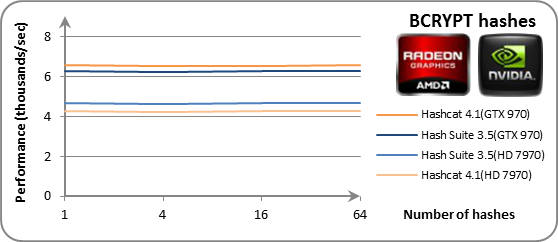
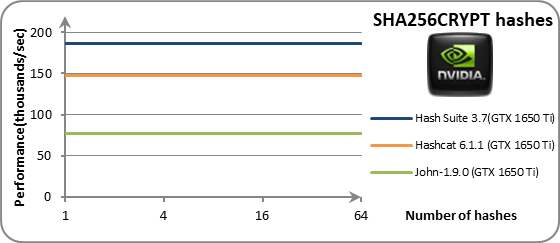
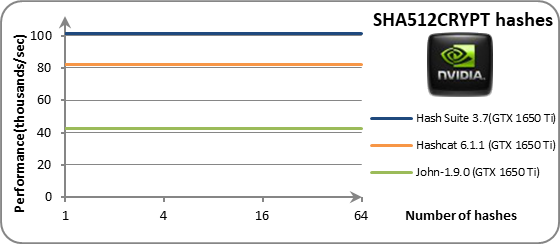
All hashes were randomly generated. The programs are sorted by average performance in first 4 columns. Performance is reported in hashes computed per second. For non-salted hashes (LM, NTLM, MD5, SHA1, SHA256, SHA512), this is the same as candidate passwords tested per second. For salted hashes (DCC, DCC2, SSHA, MD5CRYPT, BCRYPT, SHA256CRYPT, SHA512CRYPT, WPA-PSK), this is the number of candidate passwords tested per second multiplied by the number of hashes (all of which use different salts in these benchmarks). Results for salted hashes (where said multiplication was applied) are marked with asterisks (*).
Note: Demo version of PPA only permits 10 accounts.
Note: Hash Suite and Hashcat can treat the CPU as an OpenCL device (providing in many cases better performance), but unlike other CPU programs benchmarked here, it would require an OpenCL driver.
Note: John the Ripper uses a smart mode that tries more probable candidate passwords first. Other programs use a dumb mode for brute-force.
Note: John the Ripper's multi-threading support is inefficient for fast hashes (all of those benchmarked here except for DCC2, MD5CRYPT, BCRYPT, SHA256CRYPT, SHA512CRYPT, WPA-PSK), so its performance for 4 threads is not much greater than for 1 thread; much better cumulative performance of 4 processes (rather than threads) may be achieved by using --fork=4 instead.
Note: Except for SHA256CRYPT and SHA512CRYPT, an older non-AVX2 build of John the Ripper is benchmarked here; a newer AVX2 build would be up to twice faster at some of the hash types.
| Processor Name | Frequency | L1 | L2 | L3 | Ram | Other Information | |
|---|---|---|---|---|---|---|---|
 |
Intel Core i5-4670 | 3.40GHz | 64KB | 256KB | 6MB | 16GB DDR3-2400 | Windows 10 Enterprise 64-bit OpenCL Driver 5.2.0.10094 |
 |
AMD Ryzen 7 4800H | 2.9GHz | 512KB | 4MB | 8MB | 16GB DDR4-3200 | Windows 10 Professional 64-bit |
 |
Radeon HD 7970 | 1.00GHz | 16KB | 768KB | 0 | 3GB GDDR5-1375 | Driver 18.7.1 |
 |
GeForce GTX 970 | 1.20GHz | 208KB | 1.8MB | 0 | 4GB GDDR5-3505 | Driver 398.36 |
 |
GeForce GTX 1650 Ti | 1.49GHz | 512KB | 1MB | 0 | 4GB GDDR5-6000 | Driver 457.63 |
CPU Charts (click to enlarge)
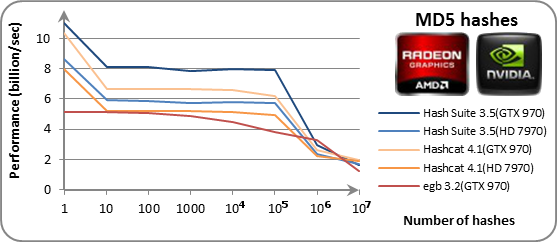
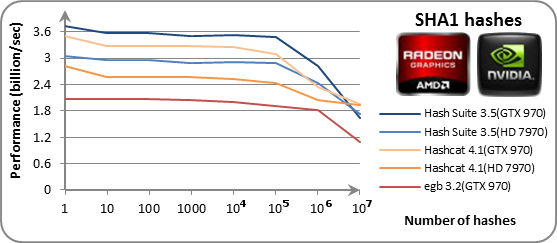
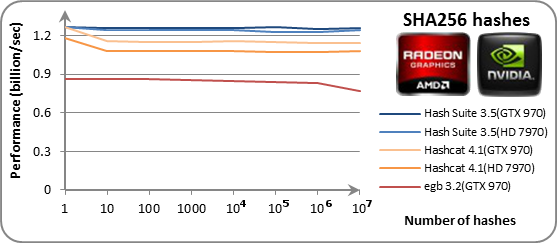
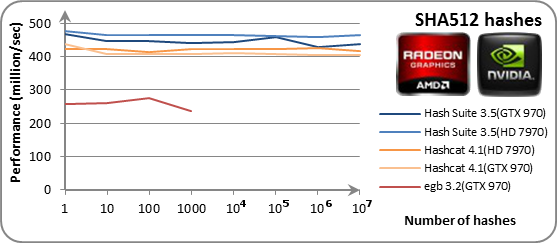
GPU Charts (click to enlarge)
More detailed performance data can be viewed here.
Compressed Wordlists
Performance of the wordlist key-provider is tested to find which compressed wordlist formats are best using 1000 NTLM hashes with and without rules support. The "wikipedia-wordlist-sraveau-20090325" file is used as reference wordlist.
| System | Format | File size | With rules | No rules |
|---|---|---|---|---|
 |
plaintext | 709MB | 241 | 19.5 |
| gz | 174MB | 233 | 9.97 | |
| zip | 174MB | 238 | 10.9 | |
| 7z | 154MB | 228 | 5.01 | |
| bz2 | 212MB | 216 | 2.72 |
For reference, the charset key-provider performs at 429 million of candidate passwords tested per second, so the wordlist key-provider with rules support has incredibly good performance (considering that it is more complicated). The use of rules with the wordlist key-provider and keeping the wordlists compressed in .gz or .zip format are highly recommended.
GPU Rules Performance
Performance of the wordlist key-provider with common rules using 1000 NTLM hashes. The "wikipedia-wordlist-sraveau-20090325" file is used as reference wordlist.
| System | Program | Rules performance |
|---|---|---|
 |
Hash Suite 3.3 | 6600 |
| oclHashcat 1.37 | 1514 |
For reference, the charset key-provider performs at 10.1 billion of candidate passwords tested per second, so the wordlist key-provider with rules support has incredibly good performance on GPU (considering that it is more complicated).